The Illusion of Invisibility
You’ve been told a lie: that the little green lock icon and a “connected” status on your VPN make you untouchable. We’ve all felt that surge of confidence after clicking the button, assuming our digital presence is now shrouded in an unbreakable cloak. But if we are so well-protected, why are we still getting hacked? Why are passwords being leaked and bank accounts drained despite the “secure tunnel”?
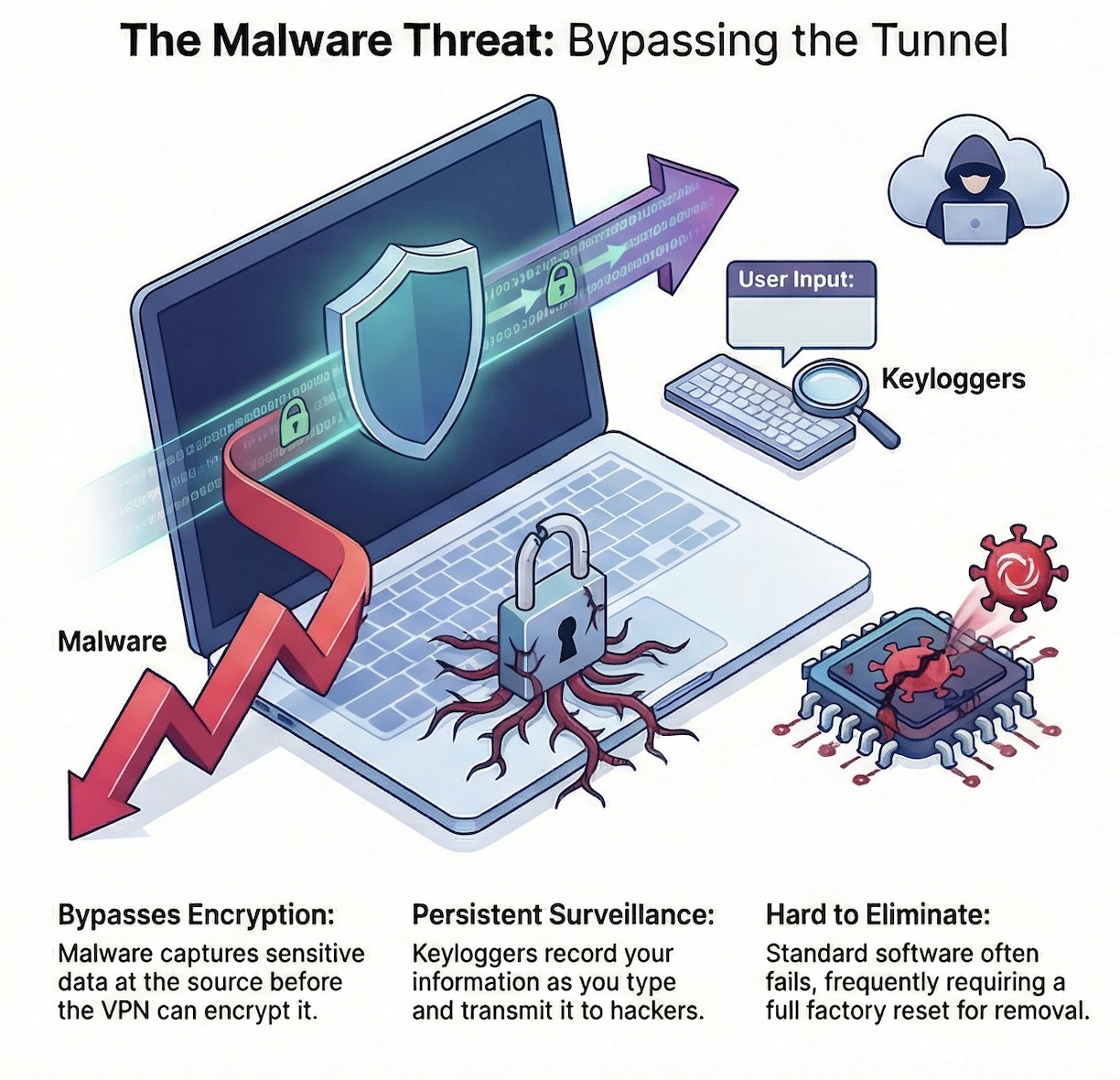
The uncomfortable truth is that encryption only protects your data while it’s traveling. It does absolutely nothing to stop the “inside man”—malware. Because malware operates from within your own system, it bypasses traditional defenses entirely, waiting in the shadows of your hard drive while you blissfully browse through your encrypted pipe.
The Malware Foothold: Why Encryption Arrives Too Late
Most of us view security as a perimeter defense, but specialized malware like keyloggers doesn’t care about your perimeter. These programs record your personal information exactly as you type it, capturing every keystroke and sensitive credential at the source. This happens long before your VPN has a chance to scramble the data.
When malicious code establishes a foothold on your device, the game is over before it even begins. It watches you in real-time, harvesting data from the “clean” side of the encryption process.
“Once malware gains a ‘foothold’ in your device, it can capture your data before it is encrypted by a VPN, essentially rendering the secure tunnel useless.”
The Great VPN Myth: Why a Tunnel Isn’t a Filter
There is a massive disconnect between what users expect and what standard VPNs actually provide. You might assume that a premium privacy service automatically scans your downloads for viruses, but for most providers, that simply isn’t true. A standard VPN is a tunnel, not a filter; it will happily transport a malicious file to your computer just as quickly as it would a harmless PDF.
To combat this, the strategy has to shift from protecting the journey to protecting the destination. Advanced tools like NordVPN’s Threat Protection Pro™ have rewritten the rules by introducing real-time download scanning. The critical nuance here is that the system identifies and blocks threats during the download process. By scanning the file before it is ever opened, the software prevents the malware from executing and gaining that initial, fatal foothold on your system.

[Explore advanced malware protection during your VPN trial]
AI-Powered Defense That Doesn’t Need a Connection
The most significant evolution in mobile and desktop security is the move toward “Stand-Alone Protection.” Traditionally, you were only as safe as your active connection. If you forgot to toggle your VPN on, you were exposed.
Threat Protection Pro™ breaks this dependency by using a sophisticated system powered by AI and machine learning to identify emerging “zero-day” risks in real-time. Crucially, this AI-driven watchdog stays on duty even when you aren’t connected to a VPN server. Whether you are tunneling your traffic or browsing locally, the system continues to proactively block trackers, intrusive ads, and malicious domains known for distributing malware. It is a persistent, intelligent layer of defense that doesn’t clock out when the VPN does.
[Explore advanced malware protection during your VPN trial]
The “Nuclear Option” vs. Proactive Prevention
Let’s talk about the reality of an infection: it is a nightmare. Once malware integrates into your system, it is notoriously difficult to evict. It can remain indefinitely, monitoring your every move and—in a final twist of irony—using your own internet connection to transmit your stolen data to third parties.
Often, standard security software isn’t enough to purge these deep-seated threats. This leaves you with the “nuclear option”: a full factory reset. Wiping your device means losing files, settings, and hours of productivity. This is why a proactive stance isn’t just a “feature”—it’s a necessity. By utilizing AI-powered scanning to stop the file before it hits your hard drive, you avoid the destructive, reactive scramble of trying to save a compromised machine.
A Rare Standard in a Crowded Market
As of March 2025, the market is flooded with VPN providers promising total privacy, yet very few have the technical infrastructure to offer native malware scanning within their applications. While many competitors offer basic web filters, they lack the specialized ability to scan downloads for hidden threats in real-time.
[Compare VPN providers with built-in malware scanning]
A survey of the current landscape reveals that major players still leave this back door open.
NordVPN remains one of the only major entities to integrate this specific native scanning capability across the entire ecosystem, including Windows, macOS, Linux, Android, and iOS.
The Future of the Layered Defense
The era of relying on a single “secure tunnel” is over. As threats become more sophisticated, our response must be equally multilayered. We are seeing a necessary shift toward “The Vanguard of Digital Defense,” where simple encryption is just one piece of a much larger puzzle. To stay safe in a landscape where malware is designed to bypass encryption, you need a strategy that includes real-time scanning, AI-driven detection, and persistent, stand-alone protection.
Is your current security setup truly proactive, or are you just waiting for the next factory reset?
[See how stand-alone VPN protection works in practice]
Disclosure & Note
This content is provided for informational purposes only and reflects general VPN testing practices at the time of writing. VPN features, trial availability, performance, and refund policies may vary by provider, platform, and region. Always review the provider’s official terms of service, privacy policy, and money-back guarantee conditions before subscribing or making a purchase decision.





